In August 2022, Apple issued a warning to its iPhone, iPad, and Mac customers. The company had learned of two serious zero-day software flaws that could allow nefarious actors to hack into users’ devices. The bugs were so significant that Apple duly advised its customers to update their products to keep the bad guys out.
But there is just one problem – the vulnerabilities have been exploited.
Life as a Target
For a majority of Apple customers, the risk from such bugs is relatively low – though it’s always advisable to maintain good security practices and keep devices up to date. However, for a subset of users, the flaws disclosed by Apple are indeed a real threat, and for some targets, the possibility of being hacked can lead to grave consequences.
All across the world, there are journalists, politicians, celebrities, dissidents, and business executives who find themselves the target of oppressive regimes, disgruntled opponents, crazed fans, or even rival operators. For these individuals, what they do on their devices can be of immense value to their enemies – and so perhaps it’s no surprise that a whole industry has grown up around the discovery and acquisition of newly discovered zero-day vulnerabilities.
The Industry of Targeted Hacking
For hackers – both state-sponsored and otherwise – there are many barriers to stealing a target’s data. From encrypted messaging services such as iMessage and Signal to biometric security systems like Face ID and Touch ID, breaking into modern devices and systems is – fortunately – very difficult.
Still, because of this fact, when a software flaw is discovered, there is unsurprisingly a market of buyers prepared to spend many hundreds of thousands of dollars to acquire it for themselves.
In 2021, Apple filed a lawsuit against Israeli company NSO Group over its Pegasus malware. The California-based tech giant claimed NSO Group had used bugs to covertly install its Pegasus onto iPhones belonging to targeted individuals. Apple claimed NSO Group was working on behalf of unnamed state operators, who were using the spyware to surreptitiously gather data from those devices.
NSO Group has previously denied governments have used Pegasus to hack devices used by reporters and civil rights figures, but the company’s software has been entangled with high-profile events such as the 2018 assassination of self-exiled Saudi Arabian journalist Jamal Khashoggi.
According to reports, a smartphone used by a confidante of Khashoggi was hacked before he was killed, exposing WhatsApp messages between the pair.
A Big Problem on a Huge Scale
Apple products are ubiquitous. At the time of writing, there are over 1.5 billion active iPhones in the world. For those concerned about being targeted, the problem can seem almost insurmountable. After all, as the Khashoggi situation illustrates, hackers don’t necessarily have to focus on a target’s device if they can manage to break into the phone of someone they communicate with.
SignalAlert can Help Keep you and your Information Safe
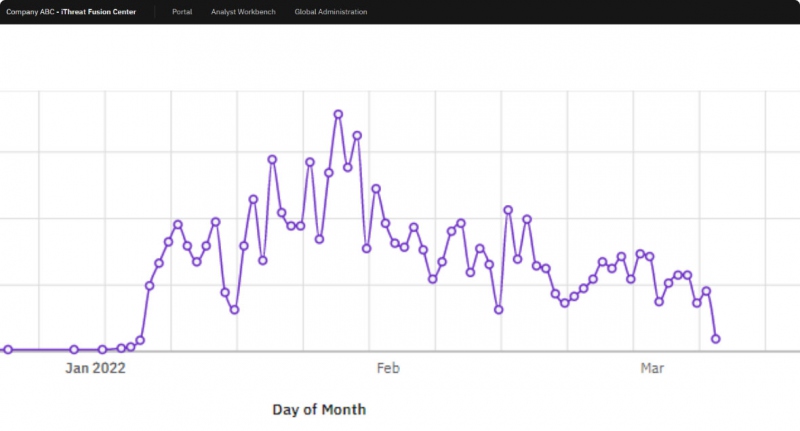
Most hack victims don’t learn about a breach until after it has occurred. Even those who expect to be targeted will have little idea their devices have been infiltrated until it’s too late. However, iThreat’s SignalAlert has been designed to help discover critical signals of a breach as quickly as possible.
By monitoring all corners of the web, SignalAlert can detect key information as it appears online. So whether that’s social media chatter or in-depth conversations on dark web forums, SignalAlert is able to capture those mentions, allowing you to take the necessary steps to better protect yourself and your data.
Additionally, with SignalAlert’s managed response tools, you’re benefiting from our 25 years of experience in helping companies tackle sensitive data leaks. With our experience and expertise, you’ll be able to understand what’s out in the world and just what you can do about it.
With so much of our lives managed via such complex digital devices, it’s almost inevitable that security vulnerabilities will occur and that the bad guys will exploit them. But that doesn’t mean you can’t take steps to protect yourself from the very worst. So make sure your iPhones, iPads, and Macs are fully patched, and use iThreat SignalAlert to make sure you know as soon as possible if your information has been compromised.