In July 2021, someone using the handle ChinaDan announced on a hacker forum that they had obtained a sizable cache of information taken from a database overseen by the Shanghai National Police. According to ChinaDan, the data included names, addresses, national ID numbers, and other personal information relating to roughly 1 billion Chinese individuals.
News of the hack spread quickly, with many suggesting it could be the biggest personal information breach of all time. Cybersecurity experts reacted quickly, downloading sample data in an effort to verify ChinaDan’s claims. Soon, researchers made a worrying discovery – much of the data seemed to relate to children, including infants as young as a year old.
The veracity of the ChinaDan incident is yet to be confirmed, in part because of China’s national censorship laws. However, the situation highlights the responsibility that organizations have when handling sensitive data, especially when it includes data for minors. Fortunately, there are steps businesses can take to help mitigate future damage when a database information leak occurs.
Understanding Database Information Leaks
From malware gangs to aggrieved former employees, database attacks can emanate from many quarters. However, regardless of the actor, the motivation is often the same: to get a hold of personally identifiable information so that it can be exploited for gain.
Many cyber criminals prize personal data because it can be used in identity theft scams. From credit card fraud to prescription drug ruses, an individual’s name, address, and more can be leveraged in a whole range of schemes, often with the victim not learning about it until it’s too late. But, as the ChinaDan situation illustrates, these risks are not unique to just to adults.
Many malicious actors will use a child’s data to propagate fraud. From opening bank accounts to applying for a driver’s license, the near-blank slate of a minor’s identity can be attractive to criminals looking to adopt a persona, especially if they hope to leverage it over an extended period. And of course, the longer a child’s details are being exploited, the more challenging it can be to unravel the damage when it finally comes to light.
Children’s Data is Often Caught up in Hacks
There has been a rise in cyber attacks against municipalities and public services in recent years. School districts, healthcare providers, and sometimes whole towns have found themselves in the clutches of criminals who want to exploit their databases. Needless to say, with hackers taking control of vast troves of personal information, it’s perhaps not surprising that children are often among the victims.
In 2021, NBC News reported hackers had published identifiable data for over 1,200 U.S. school-age children. Among the caches were details of medical conditions and the financial statuses of some families. And perhaps most concerning of all, when informed of the situation, many schools admitted they had not known the information was out in the world.
Brands Have a Choice in how They Handle Information Breaches
In 2016, ride-hailing firm Uber suffered a large-scale data breach impacting some 57 million drivers and customers. Executives at the company paid off the hackers in an attempt to cover up the incident, but a year later Bloomberg reported what had occurred. Uber was subsequently investigated and ultimately paid a fine of almost $150 million for how it handled the situation.
Hackers stole over 92 million email addresses and hashed passwords from genealogy platform MyHeritage in 2018. However, in contrast to Uber, MyHeritage opted for transparency. The company disclosed the hack right away, and established a phone line and dedicated email address to handle enquiries from concerned users – leading to praise from security experts and news outlets alike.
As these instances show, companies, brands have a choice in how they handle the fall out of a data breach. Get it right, and you can maintain public trust, despite the challenging circumstances. Get it wrong, and there can be both financial and reputational risks.
iThreat’s SignalAlert helps Organizations Respond to Information Database Leaks
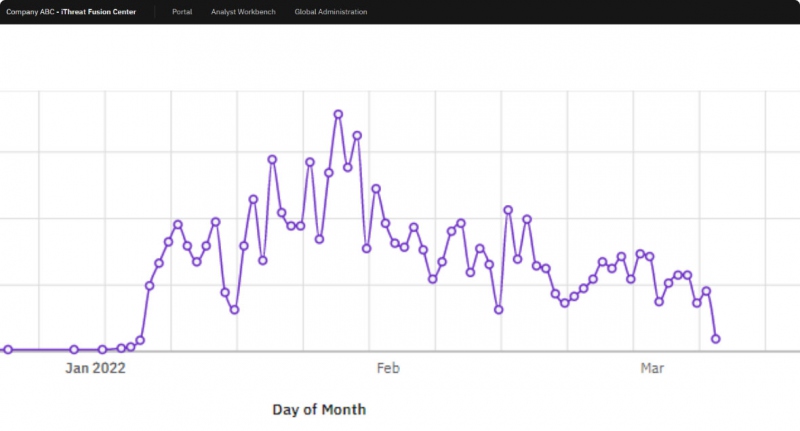
iThreat SignalAlert tracks information across the internet to deliver highly targeted intelligence that can help you manage and avert dangers as they emerge. From hacker message boards to dark web exchanges, SignalAlert is there to help your business respond to issues in real-time. And with SignalAlert’s advanced investigative tools, brands can be sure they have all they need to get to the root of the issue.
iThreat is proud to work with organizations that recognize their commitment to customer information. With SignalAlert, we make sure companies are empowered in their role as custodians of sensitive data.