Starbucks has contacted customers in Singapore, advising them of a security breach. In an email to consumers last month, the US-based coffee chain explained a malicious actor had accessed personal data belonging to users of its mobile app. The company said names, birthdates, cell phone numbers, email and home addresses were all accessed, though credit card information and account passwords were safe. Regardless, Starbucks has encouraged those affected to change their login details.
The notice from Starbucks came three days after a hacker reportedly took to a dark web market website, offering more than 500,000 records relating to almost 220,000 customers. As screenshots show, the unnamed individual promised to sell five copies of the database for $3,500 apiece. At the time of writing, at least one of those copies has sold.
Why breach Starbucks?
At first blush, it might seem odd that anyone would spend $3,500 on a data cache that doesn’t include password details for getting into customer accounts. After all, Starbucks is as much a financial services operator as it is a seller of coffee.
The company’s Starbucks Rewards program, for the uninitiated, lets users link their credit cards to a mobile app and/or physical card, allowing for quick payments in store. Those enrolled in the Rewards scheme can also order and pay ahead of time, making for an almost frictionless coffee-buying experience.
Starbucks Rewards is so popular that the program accounts for 53% of all the company’s transactions. And, when combined with active gift cards, Starbucks customers are thought to trust the company with at least $1.6 billion in stored credit at any one time. So again, what good to a hacker is a Starbucks consumer database if they can’t get at all that money?
Leveraging multiple data breaches – the art of credential stuffing
As the term suggests, credential stuffing is a process whereby nefarious actors take data from multiple breaches and put them together to access user accounts on other systems. For example, a hacker may pull someone’s username from one database, combine it with a password taken from a second system, and then use those details to get into another platform entirely. Combine this entire process with a bot network and the whole thing can run as an automated process.
Everyone is vulnerable to data breaches
Starbucks doesn’t disclose how much it spends on network security each year, but considering it’s a large multinational brand that generates billions of dollars annually, one can assume it has invested a sizable sum. But as this incident has shown, even the biggest companies can become the victim of a breach.
According to the 2021 Data Breach Report from the Identity Theft Resource Center, U.S. businesses experienced more than 1,862 data breaches last year – a 68% percent increase in 2020. The study notes 83% of attacks involved personal information.
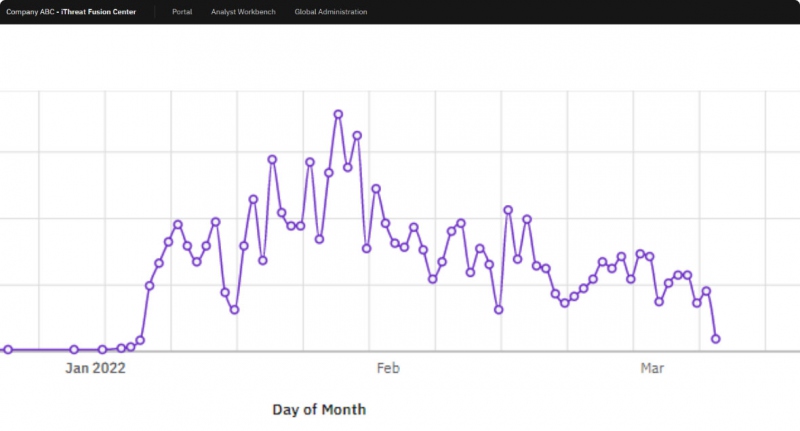
iThreat’s SignalAlert monitors the dark web to protect your users
iThreat’s SignalAlert persistently crawls the web searching for details that shouldn’t be online. Our intelligent technology monitors dark web forums, deep web marketplaces, and any number of other shadowy locations, searching for the signals that can point to a network breach. SignalAlert will then compile actionable reports, allowing you to take immediate steps to not only protect your customer’s data but also your company’s reputation.
iThreat has been in the threat-detection business for a quarter of a century. We’ve worked with hundreds of firms, helping them locate and remove countless data points from all over the internet. iThreat prides itself on its diligent and robust signal-monitoring system, which is designed to find all the digital needles – no matter the scale of the haystack.
With iThreat SignalAlert, you can be sure we’re watching out for your customers on your behalf.